A fresh leak has made the DarkSword hacking toolkit much easier to use, raising the threat level for older Apple devices that are still running iOS 18. According to a TechCrunch report published on March 23, a newer version of the tool was leaked anonymously and then posted publicly on GitHub.
Matthias Frielingsdorf, co-founder of mobile security startup iVerify, said the fallout could be serious. He noted that the leaked files are mostly built with simple HTML and JavaScript, which means the package is far less complicated than many advanced attack tools people usually associate with elite spyware or state-level operations.
That simplicity matters. In practice, someone could copy the files, drop them onto a server, and stand up an attack environment in anywhere from a few minutes to a few hours. Because the toolkit is described as essentially ready to use out of the box, even criminals with no real background in Apple internals or mobile exploitation could potentially get it running.
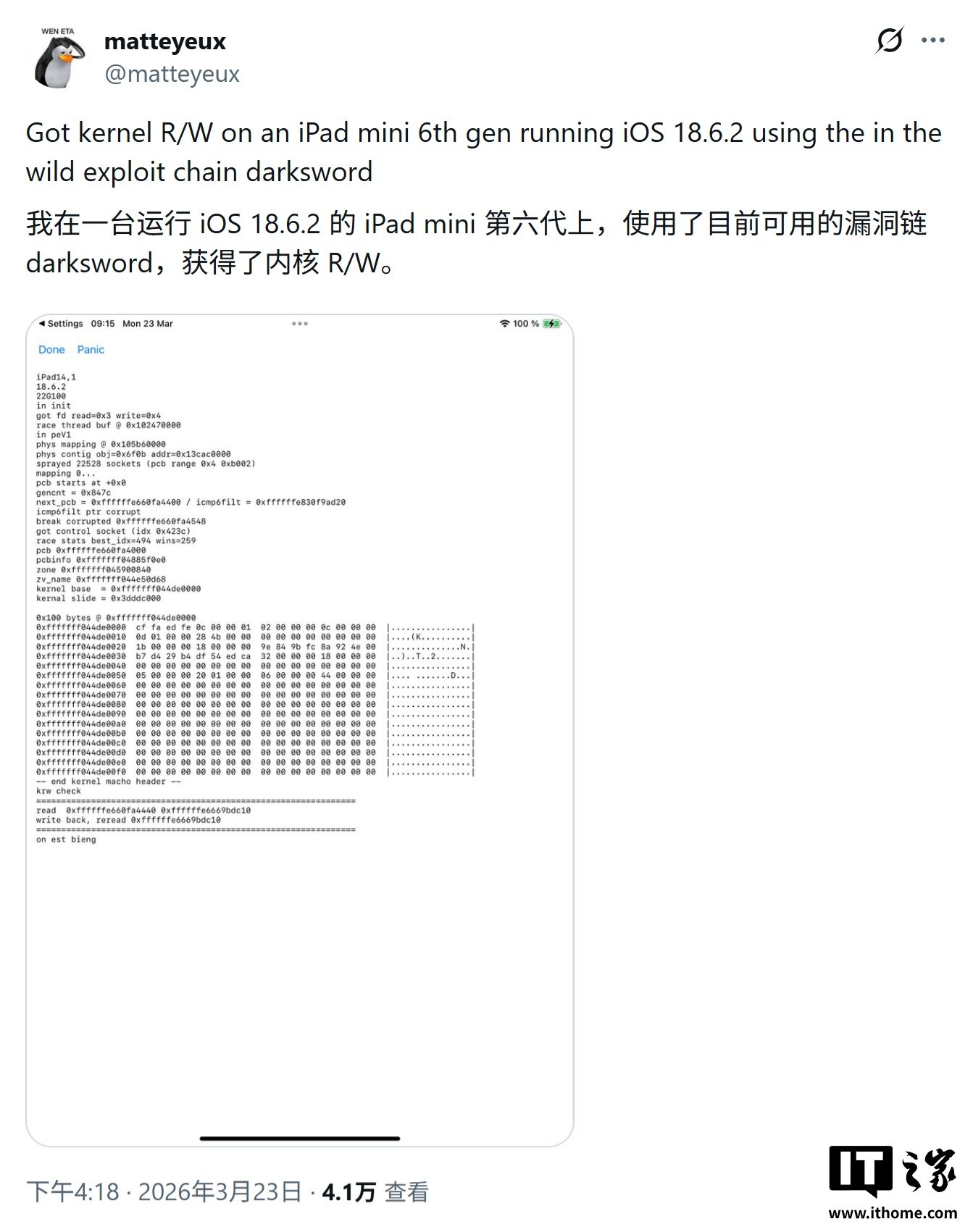
Google researchers reportedly agree with that risk assessment. Security enthusiast matteyeux also said a leaked sample available online was enough to successfully compromise an iPad mini running iOS 18, which adds weight to concerns that this is more than just theoretical chatter.
Earlier reporting said DarkSword works through the web and can deliver a zero-click exploit. In plain English, that means a victim may not need to tap anything at all. If a browser loads a malicious page, the device can reportedly be taken over silently, without any warning on screen.
The potential exposure is huge. Any iPhone still stuck on iOS 18 may be vulnerable, and Apple’s own platform figures suggest roughly a quarter of iPhones worldwide are still on that older generation. If that estimate holds, the leak could leave hundreds of millions of devices within reach of the tool.
Once the malware gets access to the file system, it reportedly shifts into post-compromise activity. Comments inside the leaked code suggest it uses HTTP requests to pull forensic-value data directly from the device.
The data haul can include contacts, text messages, call logs, and even sensitive information stored in the iOS keychain, such as saved Wi-Fi passwords. That material is then exfiltrated to a remote server controlled by the attacker, turning the compromise into a full-blown iPhone security problem rather than a limited browser incident.
Apple spokesperson Sarah O’Rourke said the company is aware of attacks targeting older operating systems. She also said Apple shipped an emergency update on March 11 for devices that can’t move to the newest iOS release.
Apple’s message is straightforward: keeping software updated remains the most important step for protecting device security. The company says fully updated devices are not exposed to this specific attack chain, and it also pointed to Lockdown Mode as an effective defense against these targeted hacking attempts.