A newly reported phishing email campaign is drawing attention because it appears to misuse legitimate Apple account alerts, allowing attackers to send messages that look far more trustworthy than the average scam email and potentially putting iPhone security at greater risk for ordinary users.
According to a report from BleepingComputer highlighted by IT Home, the attackers exploited Apple’s account-change notification process so that the messages were delivered through Apple’s own infrastructure rather than from a suspicious third-party domain. That matters because recipients are much more likely to trust an email that arrives from a recognized Apple address and carries normal authentication signatures.
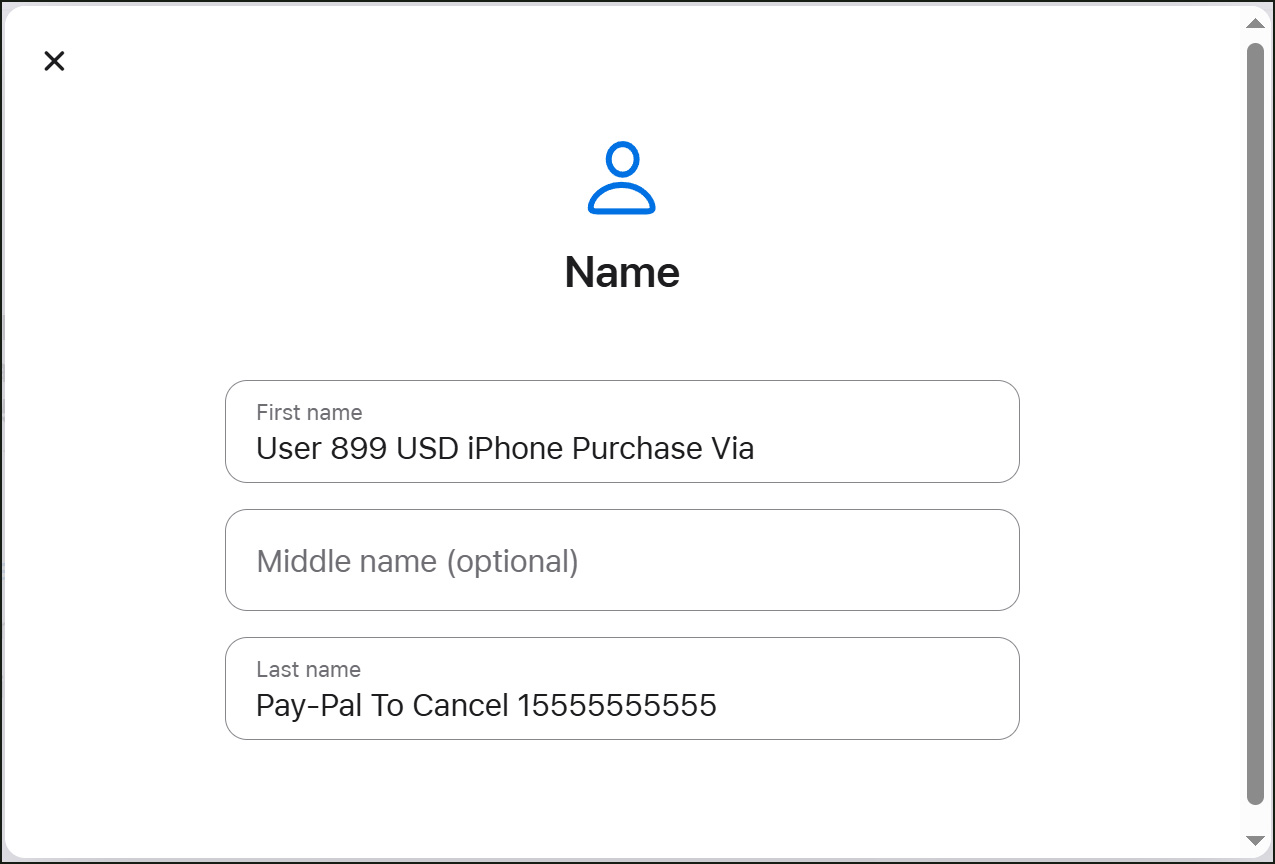
The scam emails reportedly looked like standard security notices saying account details had been updated. Hidden inside that familiar framing, though, was a fake notice claiming the user had made an $899 iPhone purchase. The message then pushed the recipient to call a phone number if they wanted to cancel the order.
Technical analysis cited in the report said the emails came from Apple infrastructure using the address appleid@id.apple.com and passed SPF, DKIM, and DMARC checks. Header information also reportedly tied the messages to an Apple mail server IP address, 17.111.110.47. Because the email itself was validly signed, it had a much better chance of slipping past spam filters and basic trust checks.
That is where the social engineering piece takes over. The phone number in the message was not an official Apple support line. Instead, it connected victims to scammers posing as Apple support staff, who then tried to convince callers that their accounts had been compromised.
From there, the fraud could escalate quickly. Victims were allegedly pressured into sharing payment details and other sensitive information, and in some cases were even asked to install remote-access software. Once that happens, the scam is no longer just about a fake purchase notice. It can turn into full device compromise, financial theft, and privacy loss.
Investigators believe the attackers created Apple IDs and then abused a loophole in the platform to trigger these messages in a way that bypassed the kinds of warning signs people are normally told to watch for. In other words, simply checking the sender address or glancing at the email headers would not have been enough here, because those details could still look legitimate.
That makes this campaign especially notable. It is a reminder that modern phishing does not always arrive with obvious spelling mistakes, fake domains, or broken formatting. Sometimes the dangerous message rides in on a real platform signal, which makes careful user behavior and official support-channel verification even more important.