![]()
Google’s Project Zero team has published new research describing a zero-click exploit chain that affected the Pixel 10 and was patched in the February 2026 security update. The report outlines how attackers could move from a media-processing flaw to full kernel read and write access without requiring the victim to interact with the device.
The first part of the chain built on earlier Project Zero work involving a Dolby Unified Decoder bug tracked as CVE-2025-54957. That library handles Dolby Digital audio formats and isn’t limited to Android, since similar code paths also appear in platforms such as iOS, Windows, and streaming devices.
What made the issue especially serious is how modern messaging workflows handle audio. On many Android phones, Google Messages may begin transcribing a received audio message before the user opens it. That means a malicious audio file could potentially trigger the bug as soon as it arrived, which is exactly why zero-click exploit chains are treated as high-risk attacks.
Project Zero said the original overwrite target used in earlier Pixel research was no longer viable on the Pixel 10 because the device introduced RET PAC protections. The researchers therefore shifted to overwriting initialization code associated with dap_cpdp_init instead of the older __stack_chk_fail route.
The second stage focused on privilege escalation. On the Pixel 9, researchers had used the BigWave AV1 decoder driver for that step, but the Pixel 10 no longer relied on it. After examining the Tensor G5 VPU driver, Project Zero researchers said they found a major flaw in about two hours.
According to the write-up, the driver exposed hardware interfaces to user space in a much more direct way than a standard V4L2 design would. It even allowed mapping MMIO register regions, which already raised the risk profile. The actual bug was in the driver’s mmap handling: it called remap_pfn_range based on the VMA size but did not properly constrain the mapping to the size of the hardware register region itself.
In practice, that opened the door to mapping arbitrary physical memory into user space, including the kernel image. Project Zero said attackers didn’t need a particularly elaborate workaround because the Pixel kernel sits at a fixed physical address, making it possible to infer its location relative to the returned mmap address instead of having to scan around for it first.
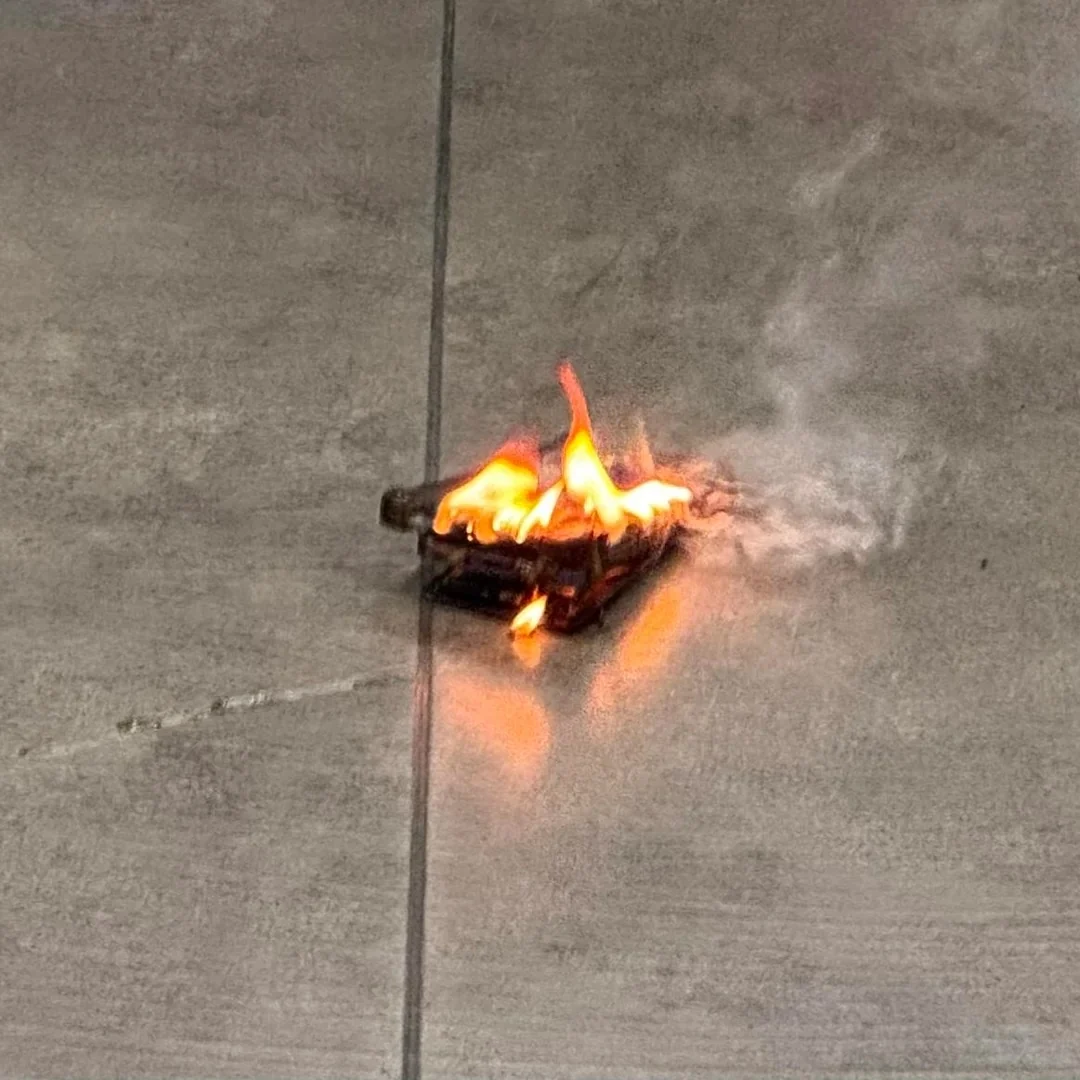
Researcher Nick Jenkins said it took only five lines of code to gain arbitrary kernel read and write access, and that the full exploit was written in less than a day. That detail underscores the larger concern here: not just the individual flaw, but the gap between the attack surface created by multimedia processing and the defensive quality of some low-level drivers.
Google said the VPU issue was reported on November 24, 2025, and fixed 71 days later in the February 2026 Pixel security bulletin. The Dolby-related part of the chain only affected devices on the December 2025 security patch level or older. For users, the practical takeaway is simple: keep the Pixel 10 updated and check the Android security patch level in Settings if there’s any doubt about whether the fix has been installed.